As we talked with our clients during our bi-annual meetings, the question again came to mind – How much should a small business budget for IT spend?
Questions to Ask
How will IT change competition in our industry?
In today’s marketplace keeping an edge above the competition can make or break the future of your business. If local customers are looking for a feature or product that you cannot provide they will look online and find it.
What will it take to exceed our customers’ expectations in a digital world?
With a broad landscape of choices available to them, what will make local businesses shine is deep customer engagement. Customer relationship management, targetted automated contact, and the consistently good products and services that technology can help provide to make this possible.
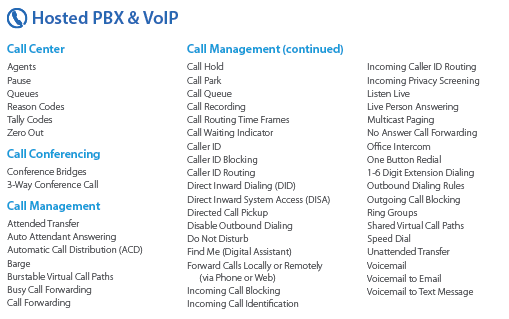
How will IT improve our operations?
Every industry now has specific software to manage the flow of business to provide repeatable and trackable results. The addition of industry-specific hardware takes the guesswork out how things get done right.
Who is accountable for IT?
Are you paying an employee or worse a manager to spend time fixing IT problems? It is always best to hire someone who is better than they are at these kinds of tasks so that they can be freed up to do what you hired them for. There are also limits to everyone’s knowledge in an alternate field, so having a next level IT provider will save headaches and downtime.
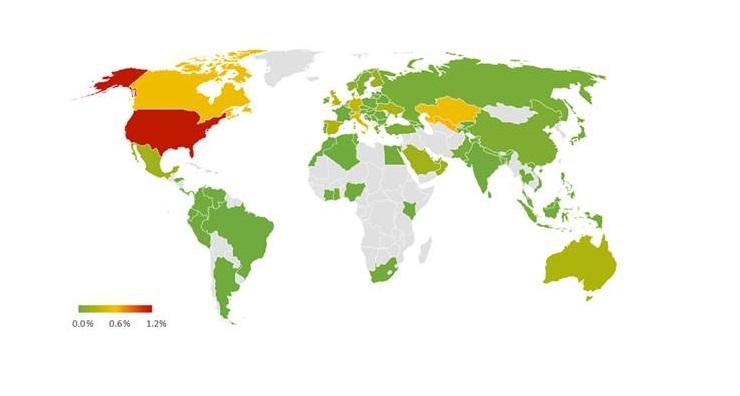
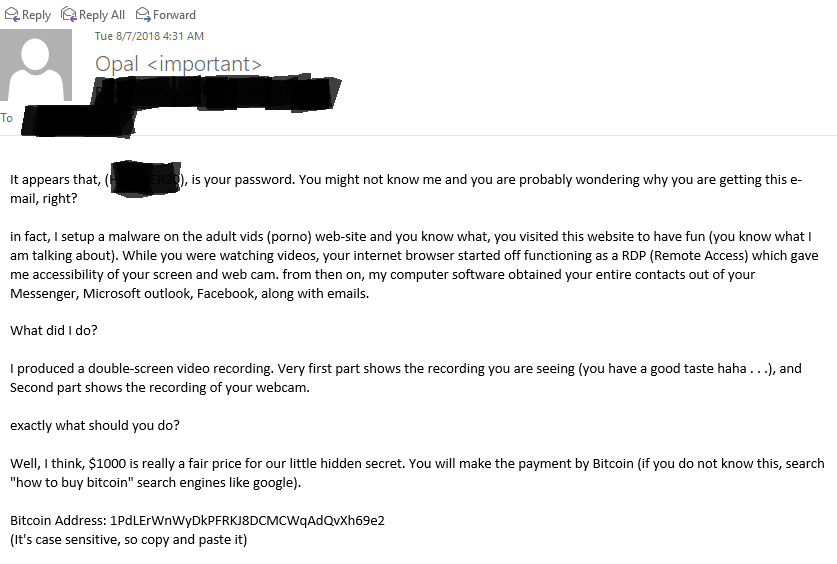
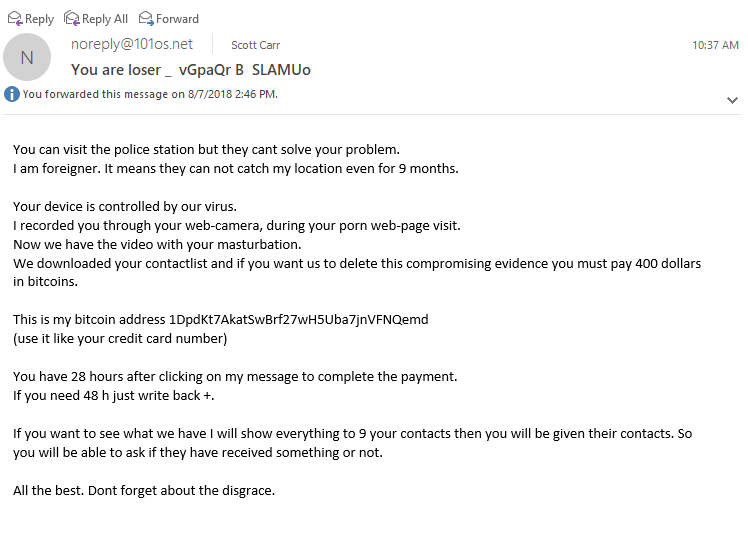
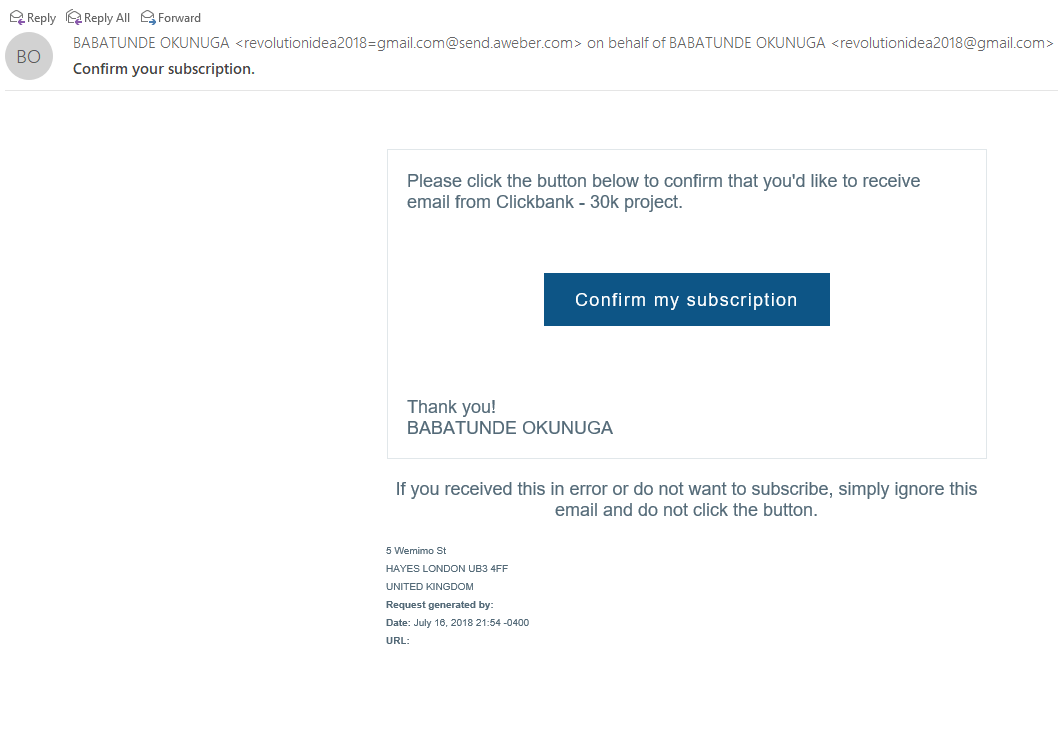
Are we comfortable with our level of IT risk?
Risks include cybercrime, downtime, employee theft, and many other possibilities. Having an IT provider with an eye for security can mitigate these risks and help eliminate the others that you never knew existed.
Boiling IT Down
According to the online studies that are out there small to medium businesses should be looking to spend around 4.1% and up to 6.9% for the smallest companies. That number has been growing about 8% year over year for the past few years. However, regardless of amount of spending, if technology investments aren’t made and used wisely, it will be reflected in that company’s returns and productivity.
Farmhouse Networking provides a free network evaluation that includes a full inventory of technology assets and 5-year technology budget.