In today’s digital age, mobile devices have become an integral part of our lives, both personally and professionally. With the increasing reliance on smartphones and tablets, businesses, especially small and medium-sized enterprises (SMBs), need to prioritize mobile device security. One effective solution for enhancing Android and iPhone security is Mobile Device Management (MDM). In this article, we will explore the benefits of MDM for SMBs, its role in enhancing Android and iPhone security, and how businesses can implement MDM to safeguard their sensitive data.
1. Understanding the Importance of Android and iPhone Security
Android and iPhone, being the most widely used mobile operating systems globally, have become a prime target for cybercriminals. With its open-source nature and extensive app ecosystem, Android devices are susceptible to various security threats, such as malware, data breaches, and unauthorized access. With its user-friendliness and built-in trust, iPhone users are easily tricked into downloading and installing malware which leads to data breaches and unauthorized access. SMBs, in particular, need to be proactive in securing their Android and iPhone devices to protect sensitive customer information, intellectual property, and maintain regulatory compliance.
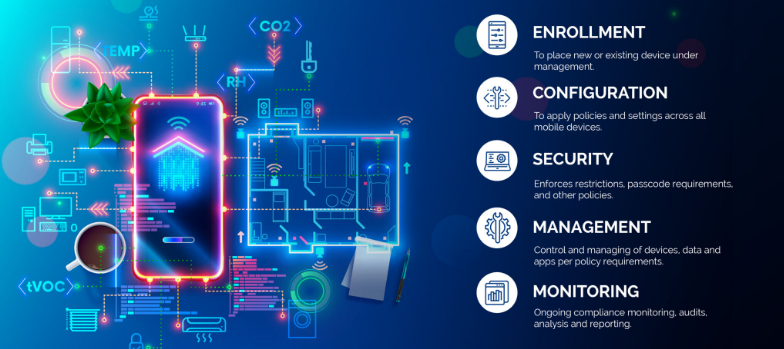
2. Introducing Mobile Device Management (MDM)
Mobile Device Management (MDM) is a comprehensive solution that enables businesses to centrally manage and secure their fleet of mobile devices, including Android and iPhone smartphones and tablets. MDM provides IT administrators with granular control over device settings, app distribution, security policies, and data management. By implementing MDM, SMBs can streamline device management, enhance data security, and ensure compliance with industry regulations.
2.1 Benefits of MDM for SMBs
- Centralized Device Management: MDM allows businesses to manage multiple Android devices from a single console, simplifying device provisioning, configuration, and updates.
- Enhanced Security: MDM enables IT administrators to enforce security policies, such as password requirements, encryption, and remote wipe capabilities, ensuring that lost or stolen devices do not compromise sensitive data.
- App Distribution and Management: With MDM, businesses can distribute and manage apps on Android devices, ensuring that only authorized and secure applications are installed.
- Secure Content and Data Management: MDM provides secure containers or workspaces on Android devices, segregating business data from personal information and enabling seamless data synchronization.
- Compliance and Reporting: MDM offers robust reporting capabilities, allowing businesses to monitor device usage, enforce compliance regulations, and generate audit trails.
3. Implementing MDM for Android and iPhone Security
Implementing MDM for Android and iPhone security involves a series of steps to ensure a seamless deployment and effective device management. Let’s explore the key considerations and best practices for SMBs looking to implement MDM.
3.1 Assessing Business Needs and Objectives
Before implementing MDM, SMBs should assess their business needs and objectives. This includes identifying the number of devices to be managed, understanding the security requirements, and evaluating the compatibility with existing IT infrastructure.
3.2 Choosing the Right MDM Solution
There are numerous MDM solutions available in the market, each with its own set of features and capabilities. SMBs should carefully evaluate different MDM vendors, considering factors such as scalability, ease of use, security features, integration capabilities, and cost-effectiveness.
3.3 Defining Security Policies and Configuration
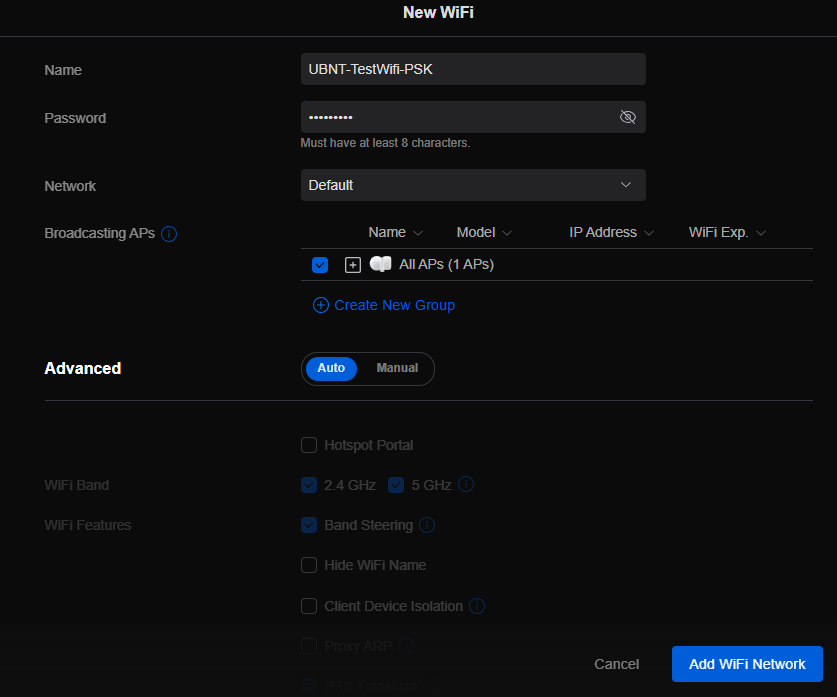
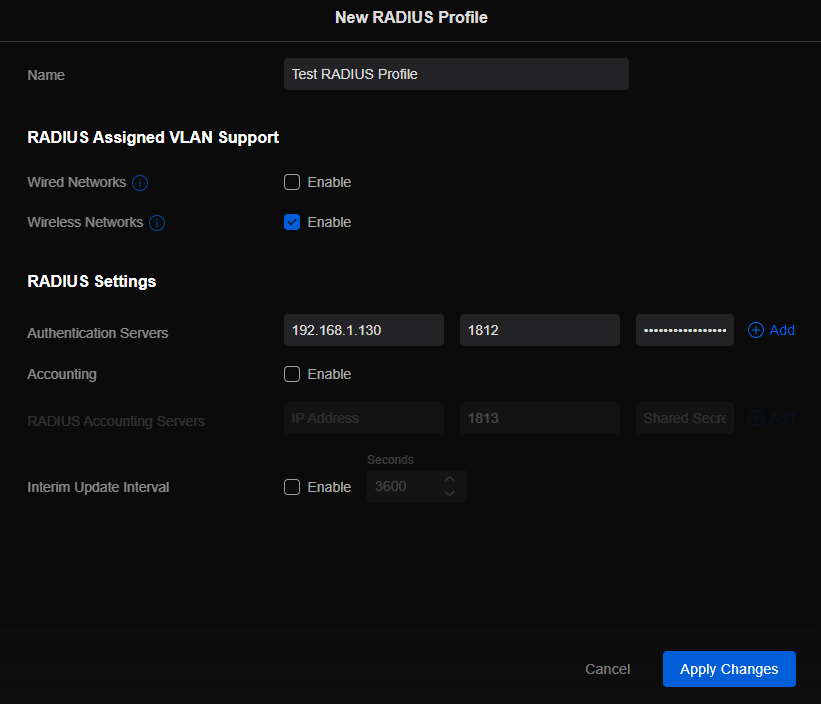
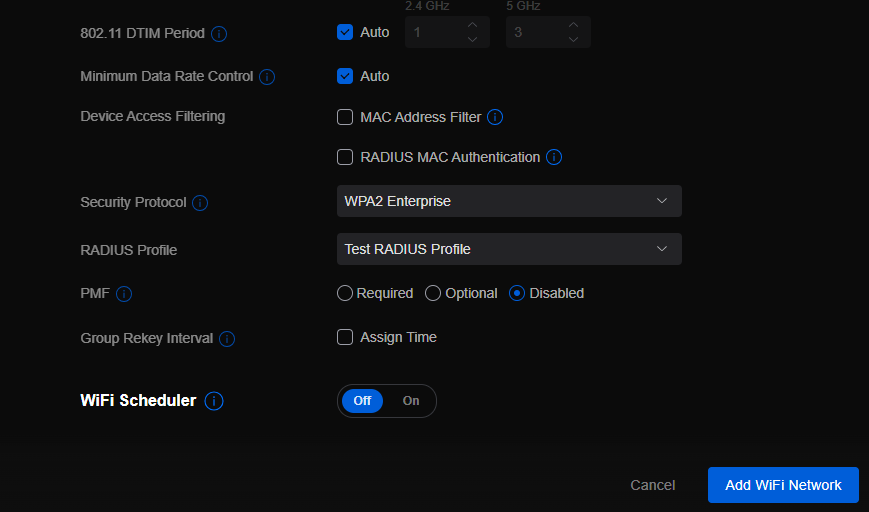
Once the MDM solution is selected, SMBs need to define security policies and configurations. This includes setting password requirements, enabling device encryption, configuring firewall settings, and defining app installation permissions. The policies should align with industry best practices and compliance regulations.
3.4 Device Enrollment and Onboarding
After defining security policies, SMBs can proceed with device enrollment and onboarding. This involves registering Android devices with the MDM system, configuring device settings, and installing necessary security profiles and certificates.
3.5 Monitoring and Maintenance
MDM is an ongoing process that requires continuous monitoring and maintenance. SMBs should regularly review security policies, update device configurations, patch vulnerabilities, and conduct security audits to ensure the effectiveness of the MDM solution.
4. Android vs. iPhone: MDM Considerations
While Android devices are more susceptible to security threats due to their open nature, it is essential to consider the unique security challenges posed by iOS devices, such as iPhones and iPads. Although iOS has built-in security features, SMBs should evaluate MDM solutions that offer comprehensive support for both Android and iOS devices to ensure consistent security across their mobile fleet.
5. The Future of MDM and Android Security
As technology evolves, the landscape of mobile device security continues to change. The future of MDM and Android security holds promising advancements, including:
- Machine Learning and AI: MDM solutions can leverage machine learning and AI algorithms to detect and prevent emerging security threats proactively.
- IoT Integration: With the rise of the Internet of Things (IoT), MDM will encompass managing and securing a broader range of devices, including wearables and smart home devices.
- Biometric Authentication: MDM solutions will increasingly utilize biometric authentication, such as fingerprint and facial recognition, for secure device access.
- Containerization and Virtualization: MDM will further enhance data security by implementing advanced containerization and virtualization techniques, isolating business data from personal information.
If your SMB is seeking to enhance Android and iPhone security by leveraging the benefits of MDM, contact us for professional assistance and guidance tailored to your specific needs.