Tech Blog
Recent Posts
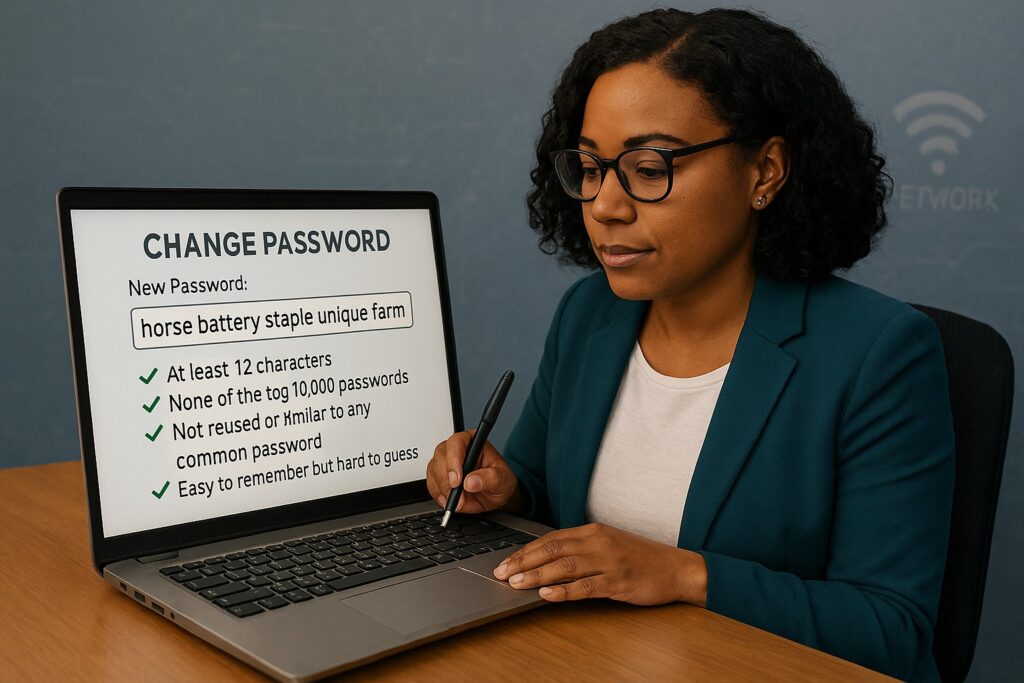
- NIST’s Password Revolution: April 3, 2026
- Staying Off the Regulator’s Radar: March 27, 2026
- AI in Your Small Business: March 27, 2026
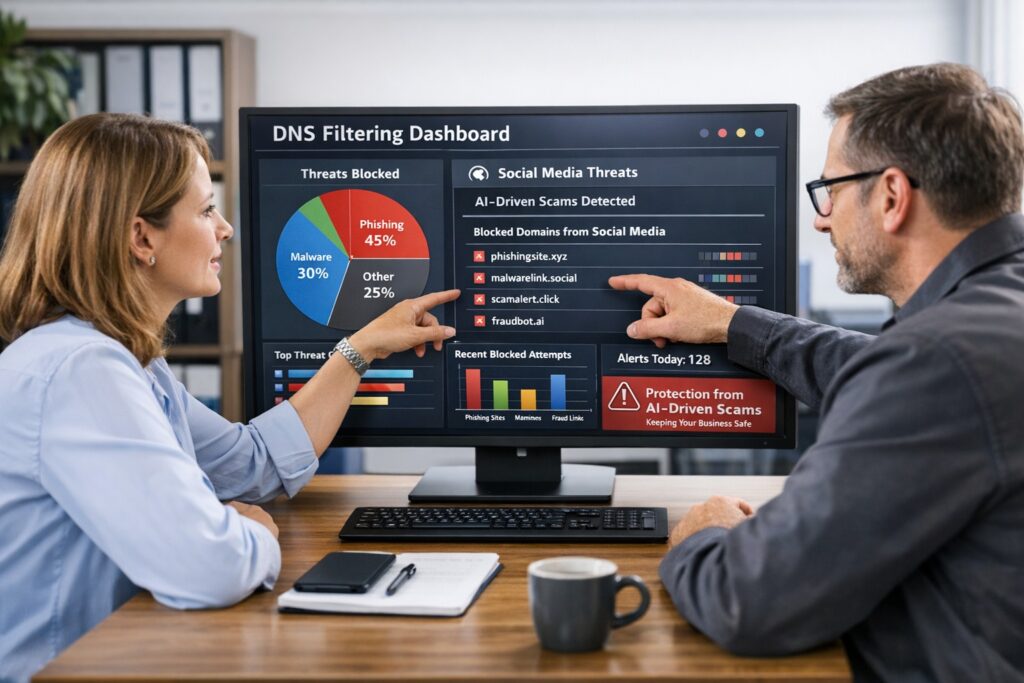
- AI Social Media Scams Are Attacking Small Businesses: March 20, 2026
- Office Network Cabling During a Remodel: March 18, 2026
Archives
- April 2026 (1)
- March 2026 (6)
- February 2026 (4)
- January 2026 (5)
- December 2025 (4)
- November 2025 (4)
- October 2025 (6)
- September 2025 (3)
- August 2025 (5)
- July 2025 (4)
- June 2025 (4)
- May 2025 (5)
- April 2025 (4)
- March 2025 (3)
- February 2025 (4)
- January 2025 (4)
- December 2024 (6)
- November 2024 (5)
- October 2024 (3)
- September 2024 (5)
- August 2024 (5)
- July 2024 (4)
- June 2024 (5)
- May 2024 (4)
- April 2024 (6)
- March 2024 (3)
- February 2024 (4)
- January 2024 (6)
- December 2023 (5)
- November 2023 (4)
- October 2023 (7)
- September 2023 (6)
- August 2023 (7)
- July 2023 (4)
- June 2023 (6)
- May 2023 (3)
- April 2023 (2)
- March 2023 (3)
- February 2023 (7)
- January 2023 (2)
- December 2022 (5)
- November 2022 (1)
- October 2022 (1)
- September 2022 (1)
- August 2022 (2)
- July 2022 (2)
- June 2022 (1)
- May 2022 (2)
- April 2022 (1)
- March 2022 (1)
- February 2022 (1)
- January 2022 (1)
- December 2021 (2)
- November 2021 (5)
- October 2021 (7)
- September 2021 (3)
- August 2021 (5)
- July 2021 (3)
- June 2021 (4)
- May 2021 (2)
- April 2021 (8)
- March 2021 (10)
- February 2021 (9)
- January 2021 (7)
- December 2020 (11)
- November 2020 (6)
- October 2020 (7)
- September 2020 (6)
- August 2020 (7)
- July 2020 (10)
- June 2020 (8)
- May 2020 (7)
- April 2020 (8)
- March 2020 (8)
- February 2020 (5)
- January 2020 (2)
- December 2019 (1)
- November 2019 (5)
- October 2019 (2)
- August 2019 (4)
- July 2019 (5)
- June 2019 (2)
- April 2019 (1)
- March 2019 (4)
- February 2019 (3)
- January 2019 (3)
- December 2018 (4)
- November 2018 (1)
- October 2018 (5)
- September 2018 (3)
- August 2018 (1)
- July 2018 (2)
- June 2018 (3)
- April 2018 (6)
- March 2018 (2)
- February 2018 (1)
- January 2018 (1)
- December 2017 (3)
- November 2017 (2)
- October 2017 (3)
- September 2017 (2)
- August 2017 (2)
- July 2017 (1)
- June 2017 (3)
- May 2017 (2)
- April 2017 (2)
- March 2017 (1)
- February 2017 (4)
- January 2017 (2)
- November 2016 (2)
- October 2016 (2)
- September 2016 (2)
- August 2016 (3)
- July 2016 (3)
- June 2016 (5)
- May 2016 (2)
- April 2016 (4)
- March 2016 (11)
- February 2016 (8)
- January 2016 (4)
- December 2015 (4)
- November 2015 (2)
- October 2015 (8)
- September 2015 (8)
- August 2015 (8)
- July 2015 (5)
- March 2015 (2)
Categories
- Access Management Solutions (3)
- Accounting (1)
- Active Directory (27)
- Adobe Cloud (2)
- AI for Small Business (7)
- AI Security for Small Business (4)
- Amazon (8)
- Apple iOS (13)
- Artificial Intelligence (19)
- Audit Logging (9)
- Automation (18)
- Azure (22)
- Azure Rights Management (2)
- Azure SQL (4)
- Backup and Restore Solutions (10)
- Battery Backup (2)
- Best Practices (24)
- Bring Your Own Device (BYOD) (55)
- Budget Talk (12)
- Business Automation (2)
- Business Continuity & Resilience (6)
- Business Efficiency Tools (1)
- Business Strategy & Planning (21)
- Cable Testing & Certification (1)
- Cabling (2)
- Calendar (6)
- Certificates (6)
- Charitable Giving & Philanthropy (1)
- Cisco (8)
- Cloud & Browser Management (1)
- Cloud Backup (7)
- Cloud Migration Solutions (17)
- Cloud Security & Compliance (35)
- Cloud Services (126)
- CMMC Assessment & Gap Analysis (2)
- CMMC Certification (8)
- CMMC Certification Costs (1)
- CMMC Level 2 Compliance Guide (2)
- Co-Managed IT (156)
- Community Engagement Applications (1)
- Compliance (142)
- Computer Repair (1)
- Copilot (1)
- cPanel (2)
- Cyber Security Training (21)
- Cybersecurity for Small Business (103)
- Daily Inspiration (34)
- Dark Web Monitoring (1)
- Data Analytics (3)
- Data Breach Prevention (5)
- Data Privacy (5)
- Data Protection (29)
- Data Security (13)
- Database Migration (2)
- Database Security (1)
- Disaster Preparedness (87)
- Distributed File Services (DFS) (1)
- DNS Filtering (14)
- DoD CMMC Budget Planning (2)
- Domain Controller (7)
- Domain Name Services (DNS) (6)
- Dynamic Host Configuration Protocol (DHCP) (4)
- Email (44)
- Email Security Solutions (5)
- Employee Security Awareness & Training (3)
- Encrypted Email (8)
- Encryption (15)
- Endpoint Detection & Response (EDR) (3)
- Endpoint Security for Small Business (7)
- Enhanced Detection & Response (16)
- Enterprise WLAN Setup (1)
- ePHI Safeguards and Encryption (1)
- Event Logs (6)
- Exchange (14)
- FAR (1)
- File Sync & Share (8)
- Folder Redirection (3)
- Freelance (4)
- Glacier Storage (5)
- Gmail (5)
- Google Android (13)
- Google Apps (19)
- Google Chrome (1)
- Government Contractor Cybersecurity (1)
- Group Policy (15)
- Hacking (1)
- Healthcare (1)
- Healthcare Regulations (1)
- Help Desk (26)
- HIPAA Compliance for Healthcare (37)
- HIPAA Risk Assessments & Audits (3)
- Hosted Email (12)
- Hosted PBX (6)
- Hybrid Cloud Security (5)
- Hyper-V (1)
- Hyperconvergence (2)
- Identity Management (1)
- Industry 4.0 (4)
- Information Security Strategies (35)
- Internet (37)
- Internet of Things (4)
- IT Asset Management (1)
- IT Cost Management (9)
- IT Infrastructure for SMBs (9)
- IT Strategy & Outsourcing (17)
- Juniper (4)
- LDAP (3)
- Leadership & Technology Decisions (2)
- Legacy Software Security (1)
- Lifecycle Management (3)
- Linux (2)
- MacOS X (1)
- Maintenance (61)
- Malware & Virus Cleanup (2)
- Managed Antivirus (21)
- Managed EDR (2)
- Managed IT Security Services (35)
- Managed IT Services (29)
- Microsoft 365 Security (18)
- Microsoft 365 Upgrade Guide (8)
- Microsoft Collaboration Tools (14)
- Microsoft Edge (1)
- Microsoft Entra ID (2)
- Microsoft Office (3)
- Microsoft Teams for Business (25)
- Mobile (11)
- Mobile Device Management (MDM) (15)
- Monitoring (15)
- Nagios Core (2)
- Network Attached Storage (NAS) (9)
- Network Firewall for Business (1)
- Network Management for SMBs (3)
- Network Policy Server (5)
- Network Security (157)
- Networking (60)
- NIST Security Framework for SMBs (11)
- Non-Profit (1)
- Office 365 (80)
- Offline Files (1)
- OneDrive for Business (3)
- Online Backup (35)
- Outlook (9)
- Password Management (27)
- Password Policy (6)
- PCI DSS (25)
- Penetration Testing (6)
- Phishing (22)
- Power Protection (11)
- PowerShell (20)
- PPPoE Router Configuration (2)
- Printer (13)
- Productivity & Workplace Tools (26)
- Quickbooks (6)
- Quotes (8)
- RADIUS (5)
- Ransomware (11)
- Registry (6)
- Remote Access (18)
- Remote Staff Collaboration (3)
- Resources (14)
- RingCentral (5)
- Risk Management for Businesses (21)
- RMM (23)
- Routing (17)
- S3 Storage (6)
- Sage 50 Accounting (Peachtree) (3)
- Scale Business (2)
- Scripts (8)
- Server Upgrades (1)
- Servers (96)
- Shadow IT Management Strategies (1)
- Sharepoint Online (3)
- SIEM Solutions (2)
- Single Sign-On (2)
- Small Business Finance (1)
- Small Business IT Optimization (10)
- Small Business Tax & Compliance (2)
- SMB Budget Optimization (18)
- SMB Data Recovery (1)
- SMB Digital Transformation (10)
- SMTP (4)
- SNMP (1)
- Software (35)
- Software as a Service (SaaS) (28)
- Software Asset Management (1)
- Solarwinds (1)
- Sophos (1)
- SPAM (9)
- SQL Server (5)
- Status (6)
- StoneEdge (1)
- Storage (30)
- Synology (9)
- Synology Active Backup (4)
- Technology As A Service (TaaS) (27)
- Terminal Server (13)
- Threat Detection & Incident Response (71)
- Tier 3 IT Support (142)
- Troubleshooting (45)
- Ubiquiti (6)
- Uncategorized (9)
- Updates (20)
- User Access & Privilege Management (2)
- Vendor Management (1)
- Video Conferencing (2)
- Virus Infection (26)
- VOIP (28)
- VPN (26)
- Vulnerability Management (3)
- Web Browser Security (1)
- Website Hosting (10)
- Website Management & Security (1)
- WHM (3)
- WiFi Security Upgrades (2)
- Windows 10 (11)
- Windows Phone (6)
- Windows Server Backup (13)
- Wireless (20)
- Wireless Network Hardening (2)
- Wordpress (2)
- Work From Home (10)
- Workflow Automation (4)
- Workstations (88)
- Zero Trust (19)
- Zoom (1)